View the “Research Report on Someone Breaching a Network” by Roshel Babayev, DeAndre Badresingh, Ron Bepat, Kanak Das, Shuaixiang Feng, and Ulises Mora here.
Category: Student Projects
Instruction Manual Project for Installing and Configuring a VirtualBox Machine
My instruction manual for Installing and Configuring a VirtualBox Machine can be found online here
500 word summary
TO: Prof. Ellis
FROM: Kanak Das
DATE: Dec, 1, 2021
SUBJECT: 500-Word Summary of Article About Network Wireless Security
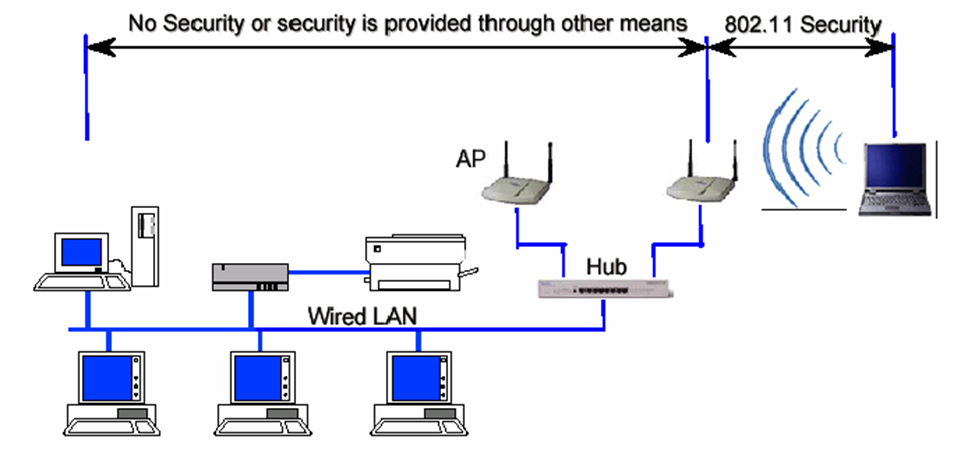
When we talk about network in computer, it also include huge responsibility in security as well as wireless security. It is one of the most important and fundamental topic in Networking. The reason this is an essential research in this topic is because Network security helps in protecting personal data, files, and others important information that is connected to devices. Increasing network security, you decrease the chance of privacy spoofing, identity or information theft and so on. Wireless network has become one of the fastest technologies for everyone’s benefit, which is a Computer Network that allows computing devices to communicate with each other without being connected through physical communications medium, such as networking cable or any involvement of wire. It is usually reply upon radio communication and wireless Network are implemented at the physical layer which is Layer 1 of the OSI model. The importance of wireless security is that it is all in one person under control. The owner can control it from anywhere nearby, without any need of wire or cable. Some of the reasons are, trusted video security solutions, commitment to quality with superior service, for personal protection.
Wireless technologies use radio frequency transmission as the means for transmitting data, whereas wired technologies use cables. Wireless technologies range from complex system, such as WLAN which is Wireless Local Area Network, when we use cell phones and have wireless headphones, through the use of Bluetooth to listen to songs, and other small devices that does not require wire. moreover, we also have, WPA which is wireless Access Point, is hardware device that allows properly equipped computing device to connect wirelessly to a network. Which can be used through router including a radio transceiver to enable wireless communication with client, and where we all use it every single day, commonly known as Wi-Fi. The transport mechanism between devices connect can also have impact on the all devices that connected to each other and any information can be shared easily through this process. Encryption is one of the major subject to talk about in wireless security, Because, all wireless computers are radio transmitters and receivers , anyone can listen to the information that are being transfer or received, that’s why it’s important to have encryption enable on wireless network. So, that way even if the other people hears about the information, they would not be able to see the information. Only people will have access are the ones with proper passwords or proper wireless configuration.
Another major topic in wireless network is Hacking. For example, if you connect to public network, it can be easily intercepted by cybercriminal, where your personal data could be at risk. Whenever there is free public wi-fi, once you connect to these fake network everything you do online is monitor by cybercriminal. Who can scan your activity such as social media log in information. Cybercriminal can even easily transfer viruses, or other unnecessary software to your computer. That can cause serious damage to your computer and can get through your personal information.
[1] “The security of cellular connections – The New York Times.” [Online]. Available: https://www.nytimes.com/2018/08/10/technology/personaltech/security-wifi-lte-data.html. [Accessed: 06-Dec-2021].
1500 Word Instruction manual
My Instruction maual for Instruction manual for Secure Computer network/Wireless/IIS web server/Share files is HERE
750-1000-Word Expanded Definition
TO: Prof. Ellis
FROM: Kanak Das
DATE: 12/05/2021
SUBJECT: Expanded Definition Term: Networking Firewall
Introduction:
Firewall is one of the important topic on Information technology. The purpose of the memo indicates that the computer or the network we use; how it can protect our information, data and applications. There are also other terms that goes along with Firewall, such as Wireless security, Network Security, Virtual private network (VPN), Virus, Ransomware. Some resources I have used for research to focus on my term is Forcepoint, Vmware, Dictionary.com. the term I have selected to focus is Firewall; A firewall is a network security device that monitors incoming and outgoing network traffic. My interest in computer is mostly network security where firewall comes up big when computer or network requires protection from hackers or malicious users.
Definition:
“A firewall protects a computer network or personal computer (PC) from attacks from hackers or malicious software, known as malware. In e-commerce, a hacker may try to access customers’ financial information or disrupt the business in some way.”[1]. Another definition is “A firewall is hardware, software, or a combination of both that monitors and filters traffic packets that attempt to either enter or leave the protected private network. It is a tool that separates a protected network or part of a network, and now increasingly a user’s personal computer (PC)”.[2]. The first definition is form the E- commerce book and the second definition is from Securing the information infrastructure book. The two definition speaks almost the same language, because both defines what firewall are supposed to do. In e-commerce definition firewall protecting their information from hackers, they see firewall as something that could protect from all kinds of threat such in the definition malware, risky software, but in reality firewall can only so much their might be some vulnerability that they are unaware of. The second definition they see that definition almost it should protect them in software level and hardware level. If an infrastructure administrator aware that when he or she is transferring packets, files, important information thru firewall it should reach its destination, but if it doesn’t, the entire transfer would backfire. From both definitions perspective it appears that each company or book define firewall as how they uses it.
Context:
It’s a quote from Cisco: “An early type of firewall device, a proxy firewall serves as the gateway from one network to another for a specific application. Proxy servers can provide additional functionality such as content caching and security by preventing direct connections from outside the network. However, this also may impact throughput capabilities and the applications they can support.”[3]. This sentence define the proxy types of firewall, which is any outside network, authorized or unauthorized network needs to be verified before getting into the cisco network. Company sees this as their way of defining the security threat, when someone from the company uses this word, they are most likely talking about an application is being transferred form one network to another.
“Another quote form Forcepoint: “We saw an opportunity to combine router and advanced firewall capabilities to strengthen security across every site and accelerate throughput. We needed a solution with centralized administration that could be easily replicated every time we added a new mobile site, easing the management burden on our IT staff.”[4]. Forcepoint security company define this as the company or the firms they host they really care about their users and their tech. The definition itself shows that they don’t only want to secure the info and data for the present, but for the future of the company as well. As times advances they want to advance their security along with it. They look for different solution for how they can manage each every users requested files, packets. Instead of having the staff and users worry about the important information they want to create a safe environment for the people and in technology as well.
Working Definition:
The research from above shows how each company treat the word firewall differently. Each and every perspective is correct, because it come down to the same meaning of how firewall works and what it should serve. My field of study Computer information Technology, IT Operation, I see firewall as one of the most fundamental being in all of computer science. Firewall is a network security mechanism that protect network or computer form solicited or unsolicited threat.
Citations:
[1]”Firewall.” Gale Encyclopedia of E-Commerce, edited by Laurie J. Fundukian, 2nd ed., vol. 1, Gale, 2012, pp. 285-286. Gale eBooks, link.gale.com/apps/doc/CX4020800178/GVRL?u=cuny_nytc&sid=bookmark-GVRL&xid=bb425618. Accessed 5 Dec. 2021.
[2]Kizza, Joseph M., and Florence M. Kizza. “Perimeter Defense: The Firewall.” Securing the Information Infrastructure, CyberTech Publishing, 2008, pp. 209-238. Gale eBooks, link.gale.com/apps/doc/CX2864600020/GVRL?u=cuny_nytc&sid=bookmark-GVRL&xid=9c1aab30. Accessed 5 Dec. 2021.
[3]“What is a Firewall?,” Cisco, 23-Jun-2021. [Online]. Available: https://www.cisco.com/c/en/us/products/security/firewalls/what-is-a-firewall.html. [Accessed: 06-Dec-2021].
[4]“NGFW Enterprise Firewall,” Forcepoint, 03-Nov-2021. [Online]. Available: https://www.forcepoint.com/product/ngfw-next-generation-firewall. [Accessed: 06-Dec-2021].
Instruction Manual on how to hack your Nintendo 3DS system
To: Prof Jason Ellis
From: Shemei John
Date: 11/17/2021
Subject: A Nintendo 3DS hack Guide
[1.0 Introduction]
This is a guide to modify your Nintendo 3DS system with custom firmware in order to personalize and customize the device. The perks of having a custom firmware are developer level and administrative level skills and access to a system, giving you more control of the devices potential capabilities, by unrestricting certain features, or accessing them otherwise. The then unrestricted firmware gives you access to custom software, applications and software themes created by others on the internet. This is for creative purposes, since you can create and install your own apps and features, as well. There are several methods to achieve this. I will be using the one most familiar to me.
[1.1 Purpose]
The purpose of this instruction manual is to practice and demonstrate administrative techniques that are familiar with Computer Information Systems. While there are a few methods to achieve this, this manual’s purpose is to also convey and explain what is being done. Popular uses for custom firmware include:
- Bypassing the region lock, allowing you to play games from other regions
- Home menu customization, using community-created themes and badges
- Modification of games (“ROM hacks”) through LayeredFS
- Save data editing, backup, and restore
- Emulation of older consoles, as well as native playback of DS and GBA games
- Installing your physical cartridges for digital use
[1.2 Intended Audience]
This manual is intended for anyone who own a Nintendo 3DS system or any student who declares a Computer Information Systems major, and are looking for practical experience learning about a computer system. It is similar to any computers system.
[1.3 Scope]
The scope of this mission is to download and install custom firmware on a stock or factory Nintendo 3DS system and proceed by performing specific functions to unlock and access restricted functions of the 3DS.
[1.4 Safety and Disclaimers]
Whenever performing any restricted tasks of any kind on any computing device there are always risks involve. It is imperative that you read and follow this manual correctly to minimize the chances of bricking.
“Bricking” is a terminology used by the computer community. Bricking means the device becomes unusable after a software, or more specifically, a firmware update was not successful. For example, the device powers on but the screen is blank and the Operating System doesn’t load. Now whenever you turn on the device the lights are on, but the screen is off forever! The risks of bricking your 3DS device has been reduced over the years significantly but there is still a chance of it happening even when you do everything correctly. This can be because of the custom firmware that was edited by others. Please be aware that you are attempting this at your own risk of bricking or voiding any warranty you may still have on your device by titivating with it. Also please be aware that since this gains restricted access to the system’s capabilities, if you attempt this method to download illegal games you could be banned from it’s network features or punished even worse.
[2.0 List of Materials and Equipment Needed]
- Computer device [a laptop is fine]
- Micro SD card reader for your computer device
- Micro SD card with at least 8G [I recommend more if you’ll need space to install more data, like downloading soft copy games. I have a 32G]
- Any unmodified Nintendo 3DS, 3DS XL, 3DS LL, 2DS system, with system firmware version of 1.0.0 – 11.3.0, anything higher will need a different method than the one in this instructional manual.
- A #00 cross-head (+) should do for the Nintendo 3DS, Nintendo 3DS XL, and Nintendo 2DS, to open up the back panel to retrieve Micro SD card.
[3.0 Directions]
[3.1] Prep devices. Check and make sure your device is compatible with this method before attempting. Make sure your devices are fully charged while performing tasks.
- Turn off your Nintendo System device and expose the Micro SD card located inside by removing the back panel screws with the mini cross head screwdriver. The screws are attached to the panel itself so be careful not to break it.
- Remove the Micro SD card and mount it to your computer
- Open the root folder of the SD card on your computer. The root folder is the main folder, or first folder of the device.
- Create a separate folder on your desktop and copy the root folder on your Micro SD card to the newly created folder on your desktop. Backing up your data before performing any kind of work on a computer is a Computer specialists’ bread and butter.
- You will then need to format your SD card to FAT32/MBR
[3.2] Acquiring boot9strap via soundhax. This is the easiest way to hack the system. Download these files from the internet. You can find them anywhere, just make sure it is the latest version. I use Github since it’s a peer-peer sharing website by users like you and I.
- Create an additional folder called boot9strap and download and extract files here
- I suggest you create a folder for each to avoid any confusion of files
- Download the latest release of SafeB9SInstaller
- Download the latest release of boot9strap
- Download the latest release of Luma3DS
- Download the latest release of universal-otherapp
[3.3] Open up your folder containing the boot9strap files and located each of the following:
- Copy the Soundhax .m4a to the root of your SD card
- Copy otherapp.bin to the root of your SD card
- Copy boot.firm and boot.3dsx from the Luma3DS .zip to the root of your SD card
[3.4] Create a folder named boot9strap on the root of your SD card. The root of the SD card is the area that the root folder is located in. Basically, the SD card itself.
- Copy boot9strap.firm and boot9strap.firm.sha from the boot9strap .zip to the /boot9strap/ folder on your SD card
- Copy SafeB9SInstaller.bin from the SafeB9SInstaller .zip to the root of your SD card
[3.5] Reinsert your Micro SD card into your 3DS system and power it on
[3.6] After you power on your device, several applications should be visible in your library, install the boot9strap by:
- Launch Nintendo 3DS Sound
- Locate /SDCARD, then play “<3 nedwill 2016” This can take several tries to be patient. If the program freezes, soft reset but powering off your device using the power button and repeat. If your versions are 9.4.0, 9.5.0 or 9.6.0, and you experience this problem, you will need to sounhax using the homebrew launcher (Separate manual). Once successful, wait for all checks to complete then press the (A) button to reset device.
[3.7] After resetting the device should be in a Luma3DS configuration window. Configure Luma3DS by:
- Using the (A) and (D-pad) to maneuver the menu, highlight “NAND or user string in System Settings” and press (START) to save and reboot if you receive an error just continue
The system will now boot to the custom firmware (Luma3DS) by default as long as the SD card is inserted. Luma3DS does not look any different from the normal HOME menu. This instruction manual is demonstrate how to apply custom firmware to the 3DS. The 3DS is now unlocked you can install additional applications that vastly simplify the loading system of the firmware. Your Device can now load the custom firmware but only from the SD card. Some additional applications essential to the firmware that will be useful can now be installed and used, such as:
- FBI (installs CIA formatted games)
- Themely (installs custom themes)
- Luma3DS Updater (updates your CFW installation easily)
- GodMode9 (multipurpose tool which can do NAND and Cartridge functions)
These are all user created programs and files shared by the community. For instance, FBI can allows the user to install files directly to your SD card simply by scanning a QR code.
4.0 Glossary
Brick – The new or expensive device that no longer works turns into a simple paper weight. The computer community uses this term to describe the result of an action taken to cause a device to stop functioning, not physically, but by loss or corruption of firmware, that causes the device to stop working.
Emulation – A reproduction or function of computing program. Often used in the video game world for old video game consoles that are now considered so small they can be replicated on a computer laptop because they do not take up a lot of space.
Firmware – specialized software created specifically for a particular device. Firmware is similar to software, the only difference is that firmware is physically written into the hardware of the device. For this reason, firmware does not require the use of an operating system to function.
Boot9strap – This program installed on your SD card allows the system to run these applications free without the use of an emulation
NAND – A chip used to store the firmware of the system
Root – The SD card itself and not the folders that is already on it. When you open or mount your SD card, that visible area is the root. The root folder is the folder that is located in this area
Boot – A term that came from the term “bootstrap” or getting your first orders. Today it essentially means to turn on your device but to boot simply means to give your computer instructions to turn it on
Soundhax – This refers to the homebrew application. This exploit gives you entry to the homebrew application that this custom firmware is basically built on without any outside assistance.
7.0 Reference List
1500 word manual instruction on secure computer network/wireless
TO: Prof. Jason Ellis
FROM: Kanak Das
DATE: 12/01/2021
SUBJECT: 1500 word instruction manual on Secure Computer network/Wireless
Encryption is one of the major subject to talk about in wireless security, Because, all wireless computers are radio transmitters and receivers, anyone can listen to the information that are being transfer or received, that’s why it’s important to have encryption enable on wireless network. So, that way even if the other people hear about the information, they would not be able to see the information. Only people will have access are the ones with proper passwords or proper wireless configuration.
Another major topic in wireless network is Hacking. For example, if you connect to public network, it can be easily intercepted by cybercriminal, where your personal data could be at risk. Whenever there is free public wi-fi, once you connect to these fake network everything you do online is monitor by cybercriminal. Who can scan your activity such as social media log in information. Cybercriminal can even easily transfer viruses, or other unnecessary software to your computer. That can cause serious damage to your computer and can get through your personal information.
Despite the fact these public networks can be harmful, there are ways to stay safe on public wi-fi. such as:
- Verify your connections, be sure to ask an employee what the actual public Wi-Fi is, in order to avoid fake network.
- Avoid checking sensitive or personal data, unless it’s necessary, avoid logging in Facebook, email and more importantly financial accounts while on public Wi-fi.
- Turn off Sharing, In your computer or the social media you are using there’s Sharing ON and OFF option. Turned that off while you are on public network.
- Turn your Wi-Fi off when you are done with your work. That can prevent falling your personal files and information on wrong hand.
So, now that there are some disadvantages of wireless security, it needs of improvement of protecting wireless data while they are in transit between a client and wireless access point.
- Techniques and Technology can be applied are:
- Use dynamic encryption key.
- Include real authentication key.
- Use strong encryption.
- Use improved cryptographic integrity protection for data frames.
- Improve session initiation.
- Use Strong Passwords.
- Have your Email connected to trusted device.
Another security technique can be applied is WPA which is Wi-fi Protected Access. WPA improve security by adding authentication Protocol for access control. It ensures the secure wireless communication. WPA support for temporal key integrity protocol TK IP which can be implemented in software with just firmware update. Along with that it also provides integrity checking using MIC, which is Message Integrity Code.
Configuring DNS on Windows, because The Domain Name System (DNS) is the protocol that makes the Internet usable by allowing the use of domain names. Its one of the safe zone to configure files or extract file.
Open the Server Manager from the task bar.
Click on DNS/ Right Click your server / select DNS Manger/ Click the Action Tab/ Select Configure a DNS Server.
-Select Configure a DNS Server in Windows Server 2012
The Configure DNS Server Wizard will come up click Next to continue and select one of the following actions:
– Create a forward lookup zone
A forward lookup zone is a DNS function that takes a domain name and resolves it to an IP address.
– Create forward and reverse lookup zones
A reverse lookup zone is a DNS function that takes an IP address and resolves it to a domain name.
– Configure root hints only
Root hints only Will have the IP addresses of DNS servers where records can be acquired.
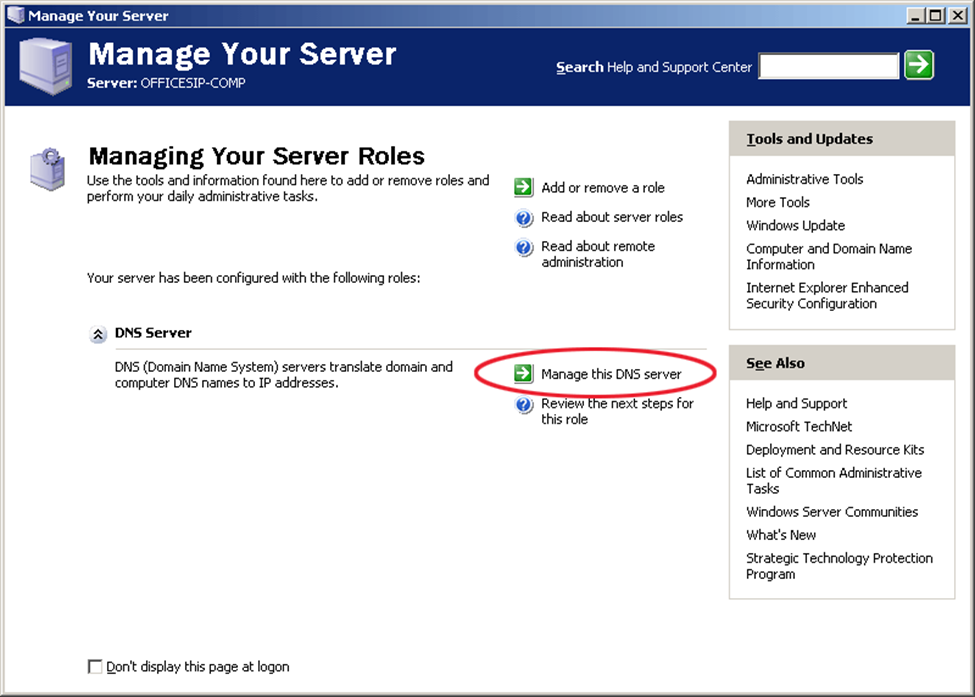
This is the Configure DNS Server Wizard screen output in Windows Server 2012
Select where the DNS data will be maintained for your network resources, and then Click Next
Selecting a Primary Server location in Windows Server 2012
Enter your new zone name, in this case, your domain and Click Next.
This is the zone name insert field when configuring DNS in Windows Server 2012
Create a new zone file or use an existing one from a different DNS server
Creating a Zone file when configuring DNS in Windows Server 2012
Next you select how your server will respond to Dynamic Updates.
Select the do not allow Dynamic Updates option while Configuring DNS in Windows Server 2012
Select whether your DNS server should forward queries or not. If you choose YES, type the IP of the server and click Next. If NO, select No, it should not forward queries and Click Next.
Select one of the options to configure forwarders when Configuring DNS in Windows Server 2012
Click Finish and you’re all set.
Completing the DNS configuration in Window Server 2012
Furthermore, one of the case study I did, to learn this implementation even better is that there is Wi-Fi provider known as Web Titan. Web titan cloud for Wi-Fi is a web content filtering and network security solution for Wi-Fi providers. This is based in London UK. Selfridges ensure that guests and staff don’t have encounter malicious sites or view inappropriate content while using their Wi-Fi network.
According to this case study this is good Wi-Fi provider for business. Some of the reasons are, it provides a safer, faster and more secure environment for your hotspot guests and finally it allows you to control the content that you allow your guests to access. You can control multiple locations and routers And Web Titan Cloud handles any volume of usage. The product has extensive reporting, easily showing you usage and traffic. It also supports dynamic IPs and works with any device that joins your network. Another feature is that all of this protection and filtering comes without any compromise to speed.
Moreover, Security in public places has become one of the major issue in Wireless security field. There have been many references on how the problem can be fixed. Top of all that VPN also known as Virtual Private Network, can be one of the strongest ways to secure our Network. This is also can be called as Layer 3 security which left the IP network vulnerable to attacks. For instance, if you need to check sensitive data such your banking or any financial account while on public Wi-Fi use Virtual Private Network. Even if a cybercriminal positions himself in a middle of your connections, your data or files will be strongly encrypted.
In conclusion, securing wireless networks can be useful and difficult and harmful at the same time, but it all depends on how carefully we are using it. As I discussed on my previous paragraph there many techniques and method we apply in order to protect our privacy. There are procedure we can follow to help ourselves in wireless network, to ensure that a wireless network is as secure as possible, network administrator should follow several guidelines.
First, and most importantly the wireless network must be encrypted as I mentioned earlier. For this purpose, it is critical to use WPA based encryption rather than WEP based encryption. Since WEP encryption is severely flawed and can be cracked with free software in jut few minutes.
Second, it is important to remember that the benefits of wireless networking come up with price. To extend this idea more, data that are traveling over wired network, wireless data are much more exposed and open. Even, if wireless data are encrypted, the absence of physical wire network, it bring the hacker one step closer to gaining access to sensitive data.
Finally, a long password should be used for network authentication. The use of very strong password may be inconvenient or bothering for users, but it will help to prevent the hacker from foiling any password cracking attack. As you can see, the use of wireless network can be very beneficial and unfavorable at the same time but it is our choice how we are going to use it for, when to use it and have pick the right moment to value our wireless technology. Technology has changed a lot throughout the years, we don’t know what the technology hold for us in future. But the way our technology growing rapidly it won’t very long until we see something amazing on technology world. Network wireless has improved a lot through the years and surely it will be even better and safer with strong encryption and protected devices, where people can access network and Wi-Fi without any worry or hesitations.
750-1000 Word Expanded definition on Networking Firewall
TO: Prof. Ellis
FROM: Kanak Das
DATE: 12/01/2021
SUBJECT: Expanded Definition Term: Networking Firewall
Firewall is one of the important topic on Information technology. The purpose of the memo indicates that the computer or the network we use; how it can protect our information, data and applications. There are also other terms that goes along with Firewall, such as Wireless security, Network Security, Virtual private network (VPN), Virus, Ransomware. Some resources I have used for research to focus on my term is Forcepoint, Vmware, Dictionary.com. the term I have selected to focus is Firewall; A firewall is a network security device that monitors incoming and outgoing network traffic. My interest in computer is mostly network security where firewall comes up big when computer or network requires protection from hackers or malicious users.
“A firewall is a network security device that monitors incoming and outgoing network traffic and decides whether to allow or block specific traffic based on a defined set of security rules.” “Advanced firewall can no longer single-handedly defend a network against today’s complex cyber threat landscape, these devices are still considered to be the foundational building block for creating a proper cybersecurity system”. From these two quoted definitions we can understand that firewall might protect network from malicious traffic, but it’s still not capable enough to stop higher complicated attack or threat. While in network firewall can be divided int two types of protection proxy and stateful, which decided what to use when, proxy can be regularly use for any kind of websites that the users might think it’s not safe website to work on. On the other hand, stateful monitors the full state of active network connections. This means that stateful firewalls are constantly analyzing the complete context of traffic and data packets.
Moreover “traditional” firewall, a stateful inspection firewall allows or blocks traffic based on state, port, and protocol. It monitors all activity from the opening of a connection until it is closed. Filtering decisions are made based on both administrator-defined rules as well as context, which refers to using information from in previous connections and packets belonging to the same connection.” And “and applications crossing through the network perimeters – especially due to the growing volume of IoT and end user devices – and less overall centralized control from IT and security teams, companies are becoming much more vulnerable to cyberattacks.” These two sentences basically talk about the fact that stateful inspection firewalls and application crossing through a specific network can be harmful for the company and for the applications itself. When data or packets being transfer form one network to another if the stateful firewall don’t investigate those packets or file a company’s or any firms information can be in wrong hands.
For example, in simple terms NAT is used to convert your IP address into your routers IP address , this is done because ipv4 which is a 32 bit IP address is limited and exhausted . Ur private IP address is not recognized by google so yuir router does the talking to the internet. It is like a cell phone which allows u to talk to “google.So” your private IP address is converted into the internet IP address with the help of net masking which u can see on seeing ifconfig which shows that your private IP address is converted into the routers IP address. Basically, when u buy internet connection you are buying an IP address that can talk to the world. ISP has globally bought a range of Ip address from IANA and it is giving u an ipaddress. So all the devices which access internet from ur home would actually be converted into the routers ip address in ur router and those packets are shoots up into the net. So router does the working of a postman when it receives reply from google and internally unmask the Ip address to determine who was the person who send that request.
In conclusion, Firewall term can be referred as where protection is needed. Whether it’s in computer, hardware, software. A firewall acts as a defensive border by helping to protect your computer from hackers, blocking malware from penetrating your system, and removing sensitive data from a compromised system. Such as stateful Firewalls scan each “packet” of data, small chunks of a larger whole, reduced in size for easy transmission, to make sure these packets don’t contain anything malicious. and interacts with the internet they come between you and the internet and thereby prevents direct connections this protects your device’s identity and keeps the network safe from potential attacks.
- “Firewall.” Fine Dictionary, http://www.finedictionary.com/firewall.html.
- “Firewall Definition and Meaning: Collins English Dictionary.” Firewall Definition and Meaning | Collins English Dictionary, HarperCollins Publishers Ltd, https://www.collinsdictionary.com/dictionary/english/firewall.
- “What Is a Network Firewall?” Fortinet, https://www.fortinet.com/resources/cyberglossary/firewall.
- “What Is a Network Firewall?” Fortinet, https://www.fortinet.com/resources/cyberglossary/firewall.
500-Word Summary on Network wirless security
TO: Prof. Ellis
FROM: Kanak Das
DATE: Dec, 1, 2021
SUBJECT: 500-Word Summary of Article About Network Wireless Security
When we talk about network in computer, it also include huge responsibility in security as well as wireless security. It is one of the most important and fundamental topic in Networking. The reason this is an essential research in this topic is because Network security helps in protecting personal data, files, and others important information that is connected to devices. Increasing network security, you decrease the chance of privacy spoofing, identity or information theft and so on. Wireless network has become one of the fastest technologies for everyone’s benefit, which is a Computer Network that allows computing devices to communicate with each other without being connected through physical communications medium, such as networking cable or any involvement of wire. It is usually reply upon radio communication and wireless Network are implemented at the physical layer which is Layer 1 of the OSI model. The importance of wireless security is that it is all in one person under control. The owner can control it from anywhere nearby, without any need of wire or cable. Some of the reasons are, trusted video security solutions, commitment to quality with superior service, for personal protection.
Wireless technologies use radio frequency transmission as the means for transmitting data, whereas wired technologies use cables. Wireless technologies range from complex system, such as WLAN which is Wireless Local Area Network, when we use cell phones and have wireless headphones, through the use of Bluetooth to listen to songs, and other small devices that does not require wire. moreover, we also have, WPA which is wireless Access Point, is hardware device that allows properly equipped computing device to connect wirelessly to a network. Which can be used through router including a radio transceiver to enable wireless communication with client, and where we all use it every single day, commonly known as Wi-Fi. The transport mechanism between devices connect can also have impact on the all devices that connected to each other and any information can be shared easily through this process. Encryption is one of the major subject to talk about in wireless security, Because, all wireless computers are radio transmitters and receivers , anyone can listen to the information that are being transfer or received, that’s why it’s important to have encryption enable on wireless network. So, that way even if the other people hears about the information, they would not be able to see the information. Only people will have access are the ones with proper passwords or proper wireless configuration.
Another major topic in wireless network is Hacking. For example, if you connect to public network, it can be easily intercepted by cybercriminal, where your personal data could be at risk. Whenever there is free public wi-fi, once you connect to these fake network everything you do online is monitor by cybercriminal. Who can scan your activity such as social media log in information. Cybercriminal can even easily transfer viruses, or other unnecessary software to your computer. That can cause serious damage to your computer and can get through your personal information.
Reference
Biersdorfer, J. “The Security of Cellular Connections.” The New York Times, The New York Times, 10 Aug. 2018, www.nytimes.com/2018/08/10/technology/personaltech/security-wifi-lte-data.html.
Biersdorfer, J. “Staying Safer on Public Networks.” The New York Times, The New York Times, 4 May 2018, www.nytimes.com/2018/05/04/technology/personaltech/staying-safer-on-public-networks.html.
Instruction Manual Project of Upgrading To windows 10 in a Business/ University Settings
My instruction manual for upgrading to windows 10 in a business/ university settings can be found online here



